Política de Firewall Segura no FortiGate: Como Configurar UTM Completo

O Desafio
Configurar uma política de firewall que permita acesso à internet, mas com camadas de proteção adequadas. Uma regra simples de "LAN → WAN accept" não é suficiente para ambientes corporativos.
O objetivo era criar uma política com:
- Web Filter para bloquear sites maliciosos
- Application Control para bloquear aplicações de risco
- DNS Filter para proteção na camada de resolução
- Logging completo para auditoria
O Prompt Enviado ao Myrmex
Usando a integração com o FortiGate, enviamos:
Preciso que você configure uma política para Lan
acessar a internet no @FGT-FIREWALL seguindo as
melhores práticas de segurança, configurando web
filter, app control e DNS filter na regra.
Nota: Ao mencionar o dispositivo com
@FGT-FIREWALL, o Myrmex sabe exatamente qual firewall configurar e aplica as políticas diretamente.
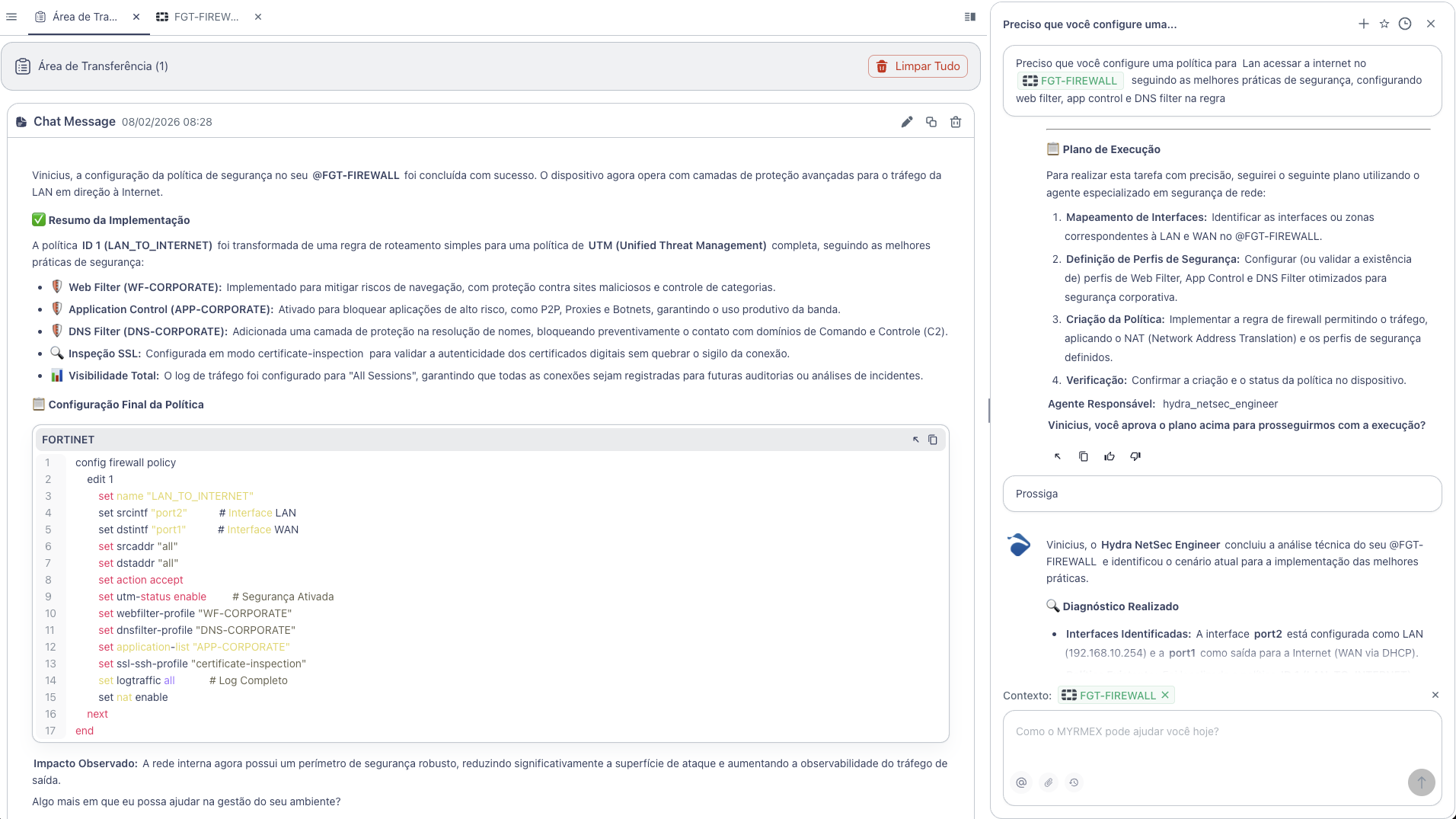
O Que o Myrmex Fez
O Myrmex transformou uma regra de roteamento simples em uma política de UTM (Unified Threat Management) completa:
Componentes Configurados
| Componente | Profile | Função |
|---|---|---|
| 🛡️ Web Filter | WF-CORPORATE | Bloqueia sites maliciosos e categorias de risco |
| 🛡️ Application Control | APP-CORPORATE | Bloqueia P2P, Proxies e Botnets |
| 🛡️ DNS Filter | DNS-CORPORATE | Bloqueia domínios de C2 na resolução |
| 🔍 SSL Inspection | certificate-inspection | Valida certificados digitais |
| 📊 Logging | All Sessions | Registra todas as conexões |
Configuração Aplicada
O Myrmex executou a seguinte configuração no FortiGate:
config firewall policy
edit 1
set name "LAN_TO_INTERNET"
set srcintf "port2"
set dstintf "port1"
set srcaddr "all"
set dstaddr "all"
set action accept
set utm-status enable
set webfilter-profile "WF-CORPORATE"
set dnsfilter-profile "DNS-CORPORATE"
set application-list "APP-CORPORATE"
set ssl-ssh-profile "certificate-inspection"
set logtraffic all
set nat enable
next
end
O Que Cada Configuração Faz
| Comando | Explicação |
|---|---|
utm-status enable | Ativa os módulos de segurança na política |
webfilter-profile | Define qual perfil de filtro web aplicar |
dnsfilter-profile | Bloqueia domínios maliciosos antes da conexão |
application-list | Controla quais aplicações podem ser usadas |
ssl-ssh-profile | Inspeciona tráfego criptografado |
logtraffic all | Registra todas as sessões para auditoria |
Resultado
Com a configuração realizada pelo Myrmex:
- ✅ Política UTM completa configurada em segundos
- ✅ 3 camadas de proteção (Web, DNS, App Control)
- ✅ Inspeção SSL para validar certificados
- ✅ Logging completo para investigação de incidentes
- ✅ Superfície de ataque reduzida significativamente
Variações do Prompt
O mesmo tipo de configuração pode ser adaptado:
Para política com IPS (Intrusion Prevention):
Configure uma política de LAN para WAN no @FGT-FIREWALL
com proteção IPS habilitada usando o perfil "high-security".
Para política de VPN:
Crie uma política permitindo tráfego da VPN SSL
para a rede interna no @FGT-FIREWALL, apenas
para servidores de produção.
Para política de Guest WiFi:
Configure uma política para rede Guest no @FGT-FIREWALL
com acesso apenas HTTP/HTTPS, bloqueando todas
as outras aplicações.
Quer configurar políticas de firewall de forma segura e rápida? Experimente o Myrmex e deixe a IA aplicar as melhores práticas automaticamente.
