Auditoría de Seguridad en MikroTik: Cómo Identificar Vulnerabilidades Automáticamente

El Desafío
Un enrutador MikroTik en producción necesita estar protegido contra amenazas. ¿Pero cómo saber si las configuraciones de seguridad son adecuadas?
El objetivo era realizar una auditoría completa de seguridad basada en normas reconocidas (CIS Benchmark), identificando:
- Usuarios con permisos excesivos
- Servicios innecesarios habilitados
- Configuraciones de firewall vulnerables
- Versiones de firmware desactualizadas
El Prompt Enviado a Myrmex
Usando la integración con el enrutador MikroTik, enviamos:
Realice una auditoría de seguridad en
@MKT-ROUTER-01 basada en CIS Benchmark.
Verifique:
Usuarios y contraseñas
Servicios habilitados (telnet, ssh, api, winbox, web)
Reglas de firewall y política de input
DNS recursivo y NTP
Versión de RouterOS y actualizaciones
Logs habilitados.
Para cada ítem: Estado (Seguro, Atención, Crítico), configuración actual y comando de corrección si es necesario.
Nota: Con solo una línea, Myrmex sabe exactamente qué equipo auditar y qué puntos verificar.
Qué Encontró Myrmex
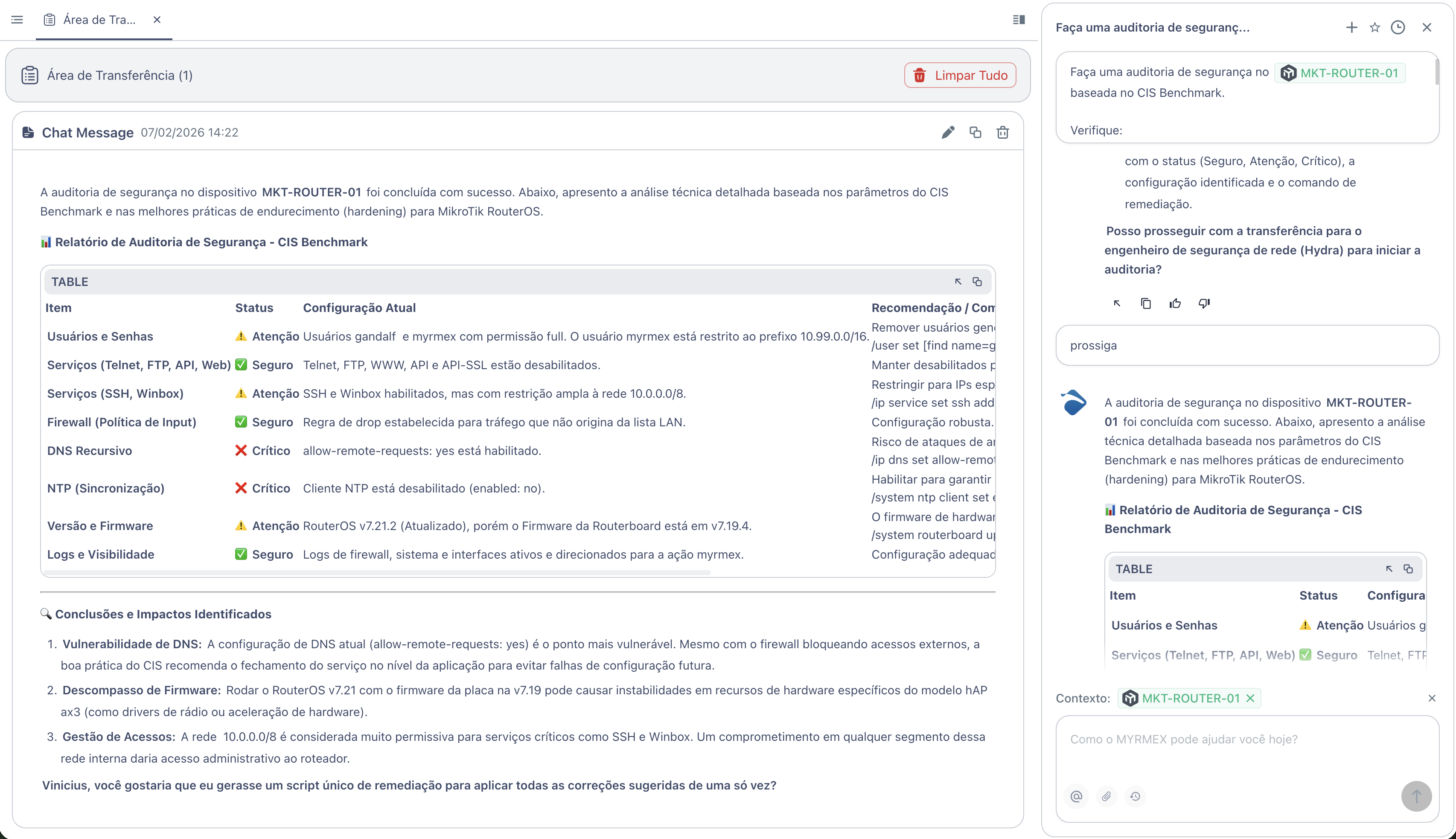
Myrmex ejecutó un análisis completo basado en CIS Benchmark y devolvió el siguiente informe:
Resumen de la Auditoría
| Ítem | Estado | Configuración Actual |
|---|---|---|
| Servicios (Telnet, FTP, API, Web) | ✅ Seguro | Telnet, FTP, WWW, API y API-SSL deshabilitados |
| Firewall (Política de Input) | ✅ Seguro | Regla de drop para tráfico fuera de la lista LAN |
| Logs y Visibilidad | ✅ Seguro | Logs de firewall y sistema dirigidos a monitoreo |
| Usuarios y Contraseñas | ⚠️ Atención | Usuarios con permiso full sin restricción de IP |
| Servicios (SSH, Winbox) | ⚠️ Atención | Habilitados, pero con restricción amplia (10.0.0.0/8) |
| Versión y Firmware | ⚠️ Atención | RouterOS v7.21.2, pero firmware de placa en v7.19.4 |
| DNS Recursivo | ❌ Crítico | allow-remote-requests=yes habilitado |
| NTP (Sincronización) | ❌ Crítico | Cliente NTP deshabilitado |
Vulnerabilidades Identificadas
❌ DNS Recursivo Abierto (Crítico)
Problema: La configuración allow-remote-requests=yes permite que el enrutador responda consultas DNS de cualquier origen, creando riesgo de ataques de amplificación.
Corrección de Myrmex:
/ip dns set allow-remote-requests=no
❌ NTP Deshabilitado (Crítico)
Problema: Sin sincronización horaria, los timestamps de los logs son incorrectos, perjudicando investigaciones de seguridad.
Corrección de Myrmex:
/system ntp client set enabled=yes servers=pool.ntp.br
⚠️ Servicios con Acceso Amplio
Problema: SSH y Winbox permiten acceso de toda la red 10.0.0.0/8. Un compromiso en cualquier segmento daría acceso administrativo.
Corrección de Myrmex:
/ip service set ssh address=IP_ADMIN/32
/ip service set winbox address=IP_ADMIN/32
⚠️ Firmware Desactualizado
Problema: RouterOS v7.21 con firmware de hardware en v7.19.4 puede causar inestabilidades.
Corrección de Myrmex:
/system routerboard upgrade
# Requiere reinicio después del comando
⚠️ Usuarios sin Restricción de IP
Problema: Usuario gandalf con permiso full sin restricción de origen.
Corrección de Myrmex:
/user set [find name=gandalf] address=X.X.X.X/32
Puntos Fuertes Identificados
Myrmex también destacó las configuraciones que ya eran adecuadas:
- ✅ Telnet, FTP, WWW, API deshabilitados - Superficie de ataque reducida
- ✅ Firewall con política de drop - Tráfico no autorizado bloqueado por defecto
- ✅ Logs centralizados - Monitoreo adecuado para fines de auditoría
Resultado
Con la auditoría realizada por Myrmex:
- ✅ 2 vulnerabilidades críticas identificadas (DNS y NTP)
- ✅ 3 puntos de atención mapeados para mejora
- ✅ 3 configuraciones seguras confirmadas
- ✅ Comandos de corrección listos para aplicar
Myrmex ofreció generar un script único de remediación para aplicar todas las correcciones de una vez.
Variaciones del Prompt
El mismo tipo de auditoría puede adaptarse:
Para auditoría enfocada en Firewall:
Audite solo las reglas de firewall de @MKT-ROUTER-01. Identifique reglas permisivas, duplicadas o sin uso.
Para verificar cumplimiento con política interna:
Verifique si @MKT-ROUTER-01 cumple con: SSH solo por llave, logs a syslog remoto, backup automático habilitado.
Para múltiples dispositivos:
Compare la configuración de seguridad entre @MKT-ROUTER-01 y @MKT-ROUTER-02. Muestre diferencias.
¿Quiere identificar vulnerabilidades antes de que sean explotadas? Pruebe Myrmex y deje que la IA audite su infraestructura automáticamente.
